The original HIPAA Security Rule was written in 2003. The iPhone was four years away. Telehealth was a niche experiment. Nobody on a clinical staff worked from home by default, and the idea that a patient might share sensitive mental health disclosures over a browser-based video call was science fiction. The rule was designed for a world of locked file rooms and on-premise servers.
That world is gone. The proposed 2024 overhaul (NPRM published January 6, 2025) finally acknowledges the gap. As of mid-2026, the rule has not been finalized — the Trump administration is still reviewing public comments and has not committed to a finalization timeline. These are still proposed rules, and the final version may differ materially. But the direction is unmistakable: regulators are moving toward mandatory MFA, stronger encryption standards, comprehensive asset tracking, and explicit remote workspace policies. These are the capabilities healthcare security is converging on regardless of the rule's outcome. Preparing now is the right call.
Before getting into the requirements, it's worth understanding why regulators are pushing this hard. The answer is in the enforcement record.
What Real Penalties Look Like: Three Cases That Should Concern You
Cerebral, the telehealth mental health startup, agreed to pay more than $7 million to the FTC after regulators found it had shared sensitive patient data with advertisers including Meta, TikTok, and Google through tracking pixels embedded on its platform. Patients seeking help for depression, anxiety, and ADHD had their health information, names, and contact details shared with ad networks without meaningful consent. The data was used for targeting. The penalty was not just financial: the FTC's order imposed restrictions that constrained how Cerebral could operate its marketing for years.
GoodRx faced a $1.5 million FTC fine for the same pattern. The company had placed tracking pixels from Facebook, Google, and Criteo on pages where users entered sensitive prescription and health condition data. That data flowed to ad platforms. GoodRx was required to never again share user health data with ad networks and to notify affected users.
These weren't rogue actors or obvious bad actors cutting corners. They were funded, staffed companies with compliance teams that simply hadn't treated analytics integrations as PHI disclosure events. The 2026 Security Rule update exists, in part, because this pattern repeated across the telehealth industry. Tracking pixels are the most visible example, but the underlying problem is broader: software systems that weren't designed with PHI boundaries as a first-class concern.
The 5 Proposed Requirements
1. Multi-Factor Authentication Would Be Required Under the Proposed Update
The original Security Rule required 'access control,' which most organizations satisfied with username and password. The proposed 2024 update would explicitly require multi-factor authentication for any workforce member accessing PHI remotely. This is not a 'should' or a 'consider' in the proposed rule - it is treated as a required safeguard, not an addressable one.
- MFA must be enforced for admin access, clinical access, and any role that touches PHI
- SMS-based MFA is acceptable but authenticator apps or hardware keys are strongly preferred
- MFA requirements extend to business associates: your vendors must also enforce MFA on systems that handle your patients' data
For a small clinic, MFA doesn't require enterprise infrastructure. A typical setup looks like this: clinical staff install an authenticator app (Google Authenticator, Authy, or Microsoft Authenticator) on their personal phones and use it to approve logins to your telehealth platform and EHR. Administrative staff with elevated access to billing or admin settings use hardware security keys (a YubiKey costs around $50) plugged into their workstation. The hardware key approach is more resistant to phishing and is the recommended approach for anyone with access to financial or multi-patient data exports.
The common objection is friction. Staff will complain. The practical response is that the friction is real but small, and it disappears within a week of adoption. The risk it eliminates, credential compromise from phishing or reused passwords, is not small. It is the leading cause of healthcare breaches.
2. Encryption Requirements: Current Rule vs. Proposed Update
Under the current HIPAA Security Rule (45 CFR 164.312), encryption is classified as 'addressable' - meaning covered entities must assess whether it is a reasonable and appropriate safeguard, and document their decision. In practice, the overwhelming majority of healthcare organizations implement encryption because the risk analysis almost always supports it. The proposed 2024 update would change encryption from addressable to required, specifying current NIST-approved algorithms (AES-256 is the effective standard). The proposed rule also addresses key management and, for higher-risk environments, field-level encryption. Until the final rule is published, encryption is best practice and effectively universal - but technically still addressable under current law.
The distinction between database encryption and field-level encryption matters more than most small practice owners realize. Think of it this way: database encryption is like locking the filing cabinet. Field-level encryption is like putting each patient file in its own locked envelope inside the cabinet. If someone breaks into the filing cabinet, database encryption gives them access to everything inside. Field-level encryption means they still need a separate key to open each envelope.
In practical terms: if your telehealth platform's database server is compromised, database-level encryption stops an attacker from reading the raw storage files. But once an attacker has valid database credentials (from a misconfigured connection string, a compromised admin account, or an insider threat), database encryption provides no additional protection. Field-level encryption means that even with database access, individual PHI fields, diagnosis codes, therapy notes, medication lists, remain encrypted until decrypted by an application layer with the correct key.
Most off-the-shelf EHRs and telehealth platforms offer database-level encryption. That meets the minimum bar today. Field-level encryption is where regulators are pointing, and it's the right question to ask any vendor you evaluate.
3. Asset Inventory Is Mandatory
The proposed update would require a current inventory of all systems, devices, and software that touch PHI. This was implied before; the proposed rule would make it explicit. The inventory must include: what the asset is, who owns it, what PHI it touches, when it was last patched, and who has access to it.
For a small clinic, this sounds burdensome. It doesn't have to be. A spreadsheet works. The point is to have a documented, maintained list you can produce during an audit. Your asset inventory should, at minimum, have these columns:
- Device Name: e.g., 'MacBook Pro - Dr. Chen' or 'Front Desk iMac'
- Device Type: Laptop, Desktop, Tablet, Phone, Server, SaaS Application
- Owner/Assigned User: Who is responsible for this device
- PHI Access Level: Read Only, Read/Write, Admin, No Access
- Last Patched: Date of last OS and software update (check quarterly)
- Encryption Status: Full disk encryption enabled yes/no, and which tool (FileVault, BitLocker)
- MFA Enforced: Yes/No for each system accessed from this device
- Location: Office, Remote, BYOD
Every laptop, tablet, and phone used to access your telehealth system goes on this list. BYOD approaches are still allowed but must be documented and meet your security minimums. The inventory is a living document. Quarterly reviews are a reasonable cadence for a small practice.
4. Enhanced Audit Logging
The updated rule requires more comprehensive audit trails. Every access to PHI, every modification, every export must be logged with user identity, timestamp, and action detail. Logs must be tamper-evident, meaning an attacker or disgruntled employee cannot modify logs to hide their tracks. The HIPAA documentation retention requirement under 45 CFR 164.316(b)(2) mandates six years for policies and procedures - as a best practice, that retention standard is commonly extended to audit logs as well, and the proposed 2024 update would make longer log retention explicit.
Most off-the-shelf EHR systems and telehealth platforms have basic audit logging. The proposed rule would require immutable, comprehensive logs. If your platform's audit trail can be edited or deleted by an administrator, it would not meet the proposed requirements — and regulators are already scrutinizing audit log practices under existing authority. Ask your vendor specifically whether audit logs are write-once and whether log integrity can be verified.
5. Remote Workspace Requirements
The original Security Rule assumed workforce members accessed PHI from a physical office. The proposed update would explicitly address the reality of remote and hybrid clinical staff. Organizations would be required to document and enforce policies around: secure home network requirements, screen privacy in shared spaces, device disposal procedures, and use of personal devices for work.
A written policy doesn't need to be 20 pages. A one-page document that your staff signs annually is sufficient, as long as it covers the right ground. At minimum, it should address:
- WiFi security: WPA3 preferred, WPA2 with a strong unique password acceptable, public or open networks never acceptable for PHI access
- Screen privacy: No working on patient records in public-facing positions, such as at a coffee shop with your screen visible to others; use a privacy screen filter on laptops used in shared spaces
- Device lock timeout: Screens must auto-lock within 5 minutes of inactivity, no exceptions
- Approved locations: List where clinical work is permitted, typically home office and clinic only, with a process for requesting exceptions
- Incident reporting: What to do if a device is lost, stolen, or accessed by an unauthorized person
The goal isn't a perfect policy. It's a documented one that demonstrates your practice has thought through the risks of remote clinical work and communicated expectations to staff.
HIPAA Penalty Structure: Current Enforcement
HIPAA penalties are tiered by culpability under existing law. Regulators have increased enforcement frequency and scrutiny for telehealth-specific violations regardless of the proposed rule's status:
- Tier 1 (unknowing violation): $100 to $50,000 per violation, $25,000 annual cap
- Tier 2 (reasonable cause): $1,000 to $50,000 per violation, $100,000 annual cap
- Tier 3 (willful neglect, corrected): $10,000 to $50,000 per violation, $250,000 annual cap
- Tier 4 (willful neglect, not corrected): $50,000+ per violation, $1,500,000 annual cap
The per-violation math is the most important number to understand. A 500-patient practice that suffers a breach because it lacked MFA could face $50,000 to $500,000 in penalties. That's not theoretical; it's the math. If a breach exposes records for all 500 patients and the cause was a missing MFA requirement (Tier 3 or 4), the per-record penalty applied across 500 violations quickly reaches six figures. Add state-level penalties, mandatory breach notification costs, and the reputational damage of a public HHS breach report, and the total impact of a single preventable incident can exceed the annual revenue of a small practice.
The Cerebral and GoodRx cases show that enforcement is not limited to data breaches in the traditional sense. A misconfigured tracking pixel that transmits patient identifiers to an ad platform is a reportable violation. The era of 'we didn't know' as a defense is shrinking.
What Small Practices Need to Do Now
- 01.Enforce MFA on every system that touches PHI: Your telehealth platform, EHR, email system, and any admin tools. If a vendor doesn't support MFA, that is a compliance gap that must be addressed, even if it means changing vendors
- 02.Document your encryption approach: Know what's encrypted at rest, what's encrypted in transit, and what algorithms are used. Request this information from every vendor in writing
- 03.Create an asset inventory: Use the column structure above. List every device, system, and software application that touches PHI. Update quarterly. This is a compliance artifact you may need to produce during an audit
- 04.Verify audit logging capabilities: Confirm your platforms log every PHI access, that logs cannot be modified by normal users, and that your retention policy aligns with best practice (six years, matching the HIPAA documentation retention standard under 45 CFR 164.316(b)(2))
- 05.Write a remote workspace policy: Use the one-page outline above. Specify home network security expectations, screen privacy rules, device requirements, and acceptable locations for clinical work
- 06.Audit your third-party scripts: Review every page in your patient portal and intake flow. If you load Google Analytics, Facebook Pixel, Hotjar, FullStory, or any other third-party script on pages where PHI appears, remove them or isolate them from PHI-containing views
- 07.Train your workforce annually: Document the training. Include the new requirements specifically
Common Compliance Gaps We See in Small Practices
- Shared admin accounts: Multiple staff using the same login makes audit logs useless. Every user needs their own credentials. 'We share the admin login to save on seats' is a compliance violation.
- Legacy EHRs without MFA: Some older EHRs simply don't support MFA. This is now a compliance gap that must be addressed, even if it means migrating systems
- Unencrypted backups: Your database is encrypted, but your nightly backup to a cloud storage bucket is not. This is a common oversight that regulators specifically look for
- No documented vendor risk assessment: The rule requires you to assess the security practices of vendors handling PHI. Most small practices skip this entirely and assume vendor BAA signature is sufficient
- Personal email for clinical communication: Staff forwarding PHI to personal email accounts to work from home is an immediate compliance violation regardless of intent
- Missing Business Associate Agreements: Every vendor that touches PHI needs a BAA. This includes your telehealth platform, EHR, billing software, and any cloud storage service used for clinical files
- Third-party tracking scripts on patient-facing pages: This is the Cerebral and GoodRx problem. If your intake form loads any script from Meta, Google, TikTok, or any analytics provider, those scripts can ingest form data including health conditions, symptoms, and patient identifiers
How to Evaluate Your Telehealth Platform's Compliance
When evaluating whether your current telehealth platform meets the 2026 standard, ask the vendor these specific questions in writing. How they answer tells you as much as what they answer.
- 01.What encryption algorithm is used for PHI at rest, and is it applied at the field level or only at the database level? Red flag: 'We use industry-standard encryption' without specifying algorithm or scope. That's marketing, not an answer.
- 02.Is MFA enforced for all user roles, and what MFA methods are supported? Red flag: 'MFA is available as an option.' Required means required. If it can be disabled per user, it is not enforced.
- 03.What is your audit log retention policy, and can logs be modified or deleted by administrators? Red flag: Any answer that includes 'administrators can manage log retention.' Immutable means immutable. Best practice is to retain logs for at least six years (matching the documentation retention standard), and the proposed 2024 update would codify longer retention explicitly.
- 04.Do you load any third-party scripts, pixels, or analytics tools on pages where patient data is visible? Red flag: Hesitation, 'we use standard analytics tools,' or not knowing the answer immediately. This should be a fast, clean 'no.'
- 05.How do you verify that your own infrastructure meets HIPAA encryption and access control requirements? Look for: third-party security audits, penetration testing cadence, SOC 2 Type II certification. Red flag: 'We follow best practices internally.'
- 06.Will you sign a Business Associate Agreement, and does it specifically address the 2026 Security Rule updates? Red flag: Offering a generic BAA template from 2019 without reviewing whether it addresses current requirements.
- 07.In the event of a security incident affecting our data, what is your notification timeline and process? The HIPAA Breach Notification Rule requires notification within 60 days. Your vendor's contractual commitment should match or exceed that.
A vendor that can answer these questions clearly, quickly, and in writing is demonstrating that compliance is part of how they built the product, not an afterthought managed by a policy document.
What to Look For in Any Telehealth Platform
When evaluating any telehealth or patient management platform for 2026 compliance, the capabilities that matter are architectural, not just documented. Look for these as baseline requirements:
- Field-level AES-256 encryption applied to PHI at rest, not just database-level encryption (best practice today and required under the proposed 2024 update)
- MFA enforced by default for all clinical and admin roles, with no path to disable it per user
- Immutable audit trails that log every PHI access event with user identity and timestamp, retained for at least six years as a best practice aligned with HIPAA documentation retention standards
- Zero third-party tracking scripts on any patient-facing page, including intake forms and appointment scheduling
- BAA included with every plan tier, not offered as a premium add-on
- Automated security testing integrated into the deployment pipeline, so new releases don't introduce regressions
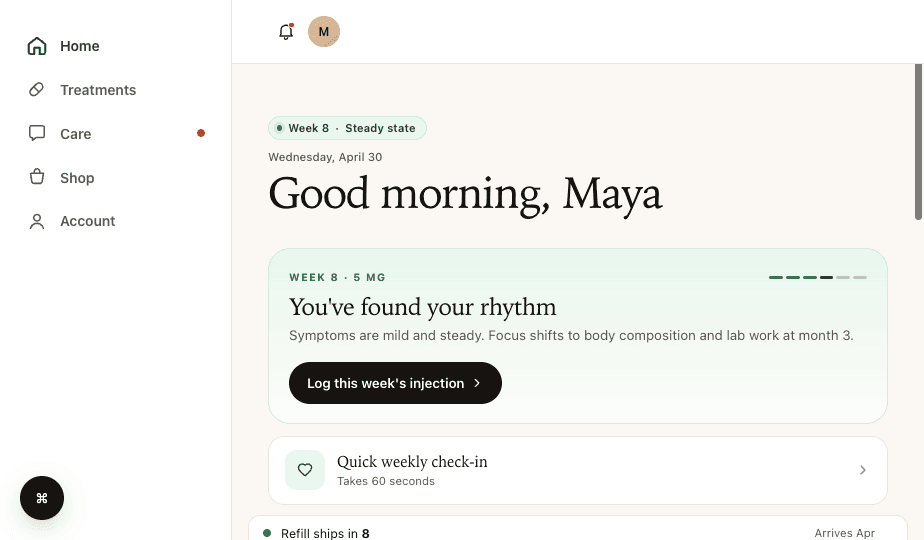
Thimble Hub was built with these requirements as the foundation rather than as a compliance layer added afterward. If you're evaluating your current platform or comparing alternatives, these criteria are a reasonable starting checklist. Any platform built after 2022 with HIPAA compliance as a stated goal should be able to address all of them.
Frequently Asked Questions
- What should I do first if I haven't started preparing?
- Prioritize in this order: (1) Enable MFA on every system that touches PHI today, starting with your telehealth platform and EHR. This is the single highest-impact action and takes hours, not weeks. It is required under the proposed 2024 update and is the right security practice regardless. (2) Audit third-party scripts on patient-facing pages. Remove or isolate any analytics, advertising, or session recording tools from pages where PHI appears. (3) Build your asset inventory. Start a spreadsheet and spend two hours listing every device and system. Imperfect and existing beats perfect and not started. (4) Write a one-page remote workspace policy and have staff sign it. (5) Request written answers on encryption and audit logging from every vendor you use. The goal is to eliminate the most common, most penalized gaps first, then systematically address documentation and vendor management.
- When do the updated HIPAA Security Rule requirements go into effect?
- The Security Rule update was proposed in late 2024 (published in the Federal Register January 6, 2025) and has not yet been finalized as of mid-2026. The Trump administration is reviewing more than 4,700 public comments and has not committed to a finalization timeline. No compliance deadline has been set. However, the direction of the proposed rule reflects security capabilities that regulators are scrutinizing under existing authority, and the Cerebral and GoodRx enforcement actions show FTC action under existing rules is active. Waiting for a final rule before preparing is not a sound strategy.
- Do I need MFA for every employee at my clinic?
- Yes, for anyone who accesses PHI, under the proposed 2024 Security Rule update. This includes clinical staff, admin staff, billing, and anyone else with login credentials to systems containing patient data. Front desk staff who access scheduling systems that show patient names and contact information are included. External contractors with system access are included. Under the proposed rule: if the login can reach PHI, MFA would be required. Even under the current rule, MFA is widely considered a necessary safeguard and will be required once the final rule is published.
- What's the difference between database encryption and field-level encryption?
- Database encryption protects the entire database file from unauthorized access at the storage level, like locking the filing cabinet. Field-level encryption protects individual data fields within records, so even if someone gains valid database access through compromised credentials or an insider threat, individual PHI fields remain encrypted. Think of it as each patient file having its own locked envelope inside the locked cabinet. Field-level is the emerging best practice and the direction the updated rule is pointing toward.
- Can I still use BYOD (personal devices) for clinical work under the new rules?
- Yes, but you must document and enforce BYOD policies that include device security requirements (encryption, lock timeout, approved apps), acceptable use, disposal procedures when a device is no longer used, and remote wipe capabilities if a device is lost or stolen. Informal BYOD, where staff use personal devices without any documented policy or security minimums, is not acceptable.
- How do I know if my telehealth vendor is HIPAA compliant under the 2026 rule?
- Ask them in writing using the seven questions listed in the vendor evaluation section of this post. Specifically: what encryption they use at what level, whether MFA is enforced or just available, how audit logs are protected from modification, whether any third-party scripts run on patient-facing pages, and whether they'll sign a BAA that references the 2024 Security Rule changes. A compliant vendor can answer these questions clearly and quickly. Vague answers that use phrases like 'industry-standard security' without specifics are a red flag.
- Is a tracking pixel really a HIPAA violation?
- It can be, and regulators have demonstrated they will pursue it. If a tracking pixel transmits data from a page where a patient enters health information, such as symptoms on an intake form, a prescription search on a health platform, or a condition selection on a scheduling page, that transmission may constitute a disclosure of PHI to an unauthorized third party. The Cerebral and GoodRx cases were pursued under FTC authority rather than HIPAA directly, but HHS has issued guidance making clear that tracking technologies on patient-facing platforms are subject to HIPAA requirements. The safest position is no third-party scripts on any page where PHI appears.
Building a telehealth brand?
Thimble Hub gives you the checkout, intake, patient portal, and EHR-routing infrastructure so you can launch in weeks, not quarters. Modular, HIPAA-ready, no lock-in.